Threats of Cybersecurity
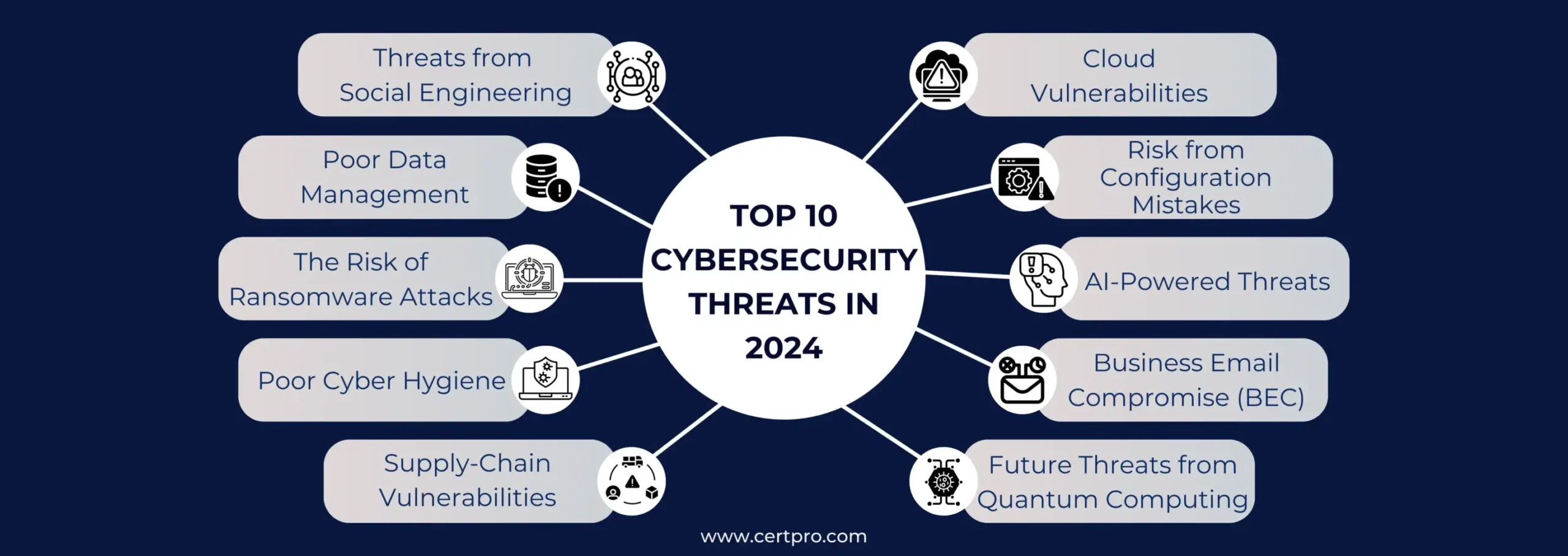
Cybersecurity threats are malicious activities that aim to compromise the security of systems, networks, and data. These threats can lead to financial loss, identity theft, reputational damage, and even national security risks. Below are the major cybersecurity threats, their working mechanisms, and how to mitigate them.
1. Malware (Malicious Software)
Definition: Malware is software designed to infiltrate or damage a system without the user’s consent.
Types of Malware:
- Viruses – Attach themselves to files and spread when executed.
- Worms – Spread without user interaction, often through networks.
- Trojans – Disguise themselves as legitimate software but carry malicious code.
- Spyware – Secretly gathers user information without consent.
- Adware – Displays unwanted advertisements that can lead to malware infections.
How It Works:
- A user downloads an infected file or visits a compromised website.
- The malware installs itself and begins stealing data, corrupting files, or spying on the user.
Mitigation:
✅ Use updated antivirus software
✅ Keep your system and applications updated
✅ Avoid downloading files from untrusted sources
2. Phishing Attacks
Definition: Phishing is a type of cyberattack where attackers impersonate legitimate entities to steal sensitive information like usernames, passwords, or financial details.
Types of Phishing:
- Email Phishing – Fake emails pretending to be from banks or companies.
- Spear Phishing – Targeted attacks against individuals or organizations.
- Whaling – Phishing attacks targeting high-profile individuals like CEOs.
- Smishing & Vishing – Phishing via SMS (Smishing) or phone calls (Vishing).
How It Works:
- The victim receives an email or message with a malicious link.
- Clicking the link redirects to a fake website resembling a trusted entity.
- Victim enters credentials, which are stolen by the attacker.
Mitigation:
✅ Verify email senders before clicking links
✅ Look for misspellings and unusual email domains
✅ Enable Multi-Factor Authentication (MFA) for added security
3. Ransomware
Definition: Ransomware is a type of malware that encrypts a victim’s data and demands a ransom for decryption.
How It Works:
- Attackers gain access through phishing emails, unsecured networks, or exploit vulnerabilities.
- The ransomware encrypts critical files, making them inaccessible.
- A ransom note appears, demanding payment (often in Bitcoin) for the decryption key.
Famous Ransomware Attacks:
- WannaCry (2017) – Affected over 200,000 computers globally.
- NotPetya (2017) – Caused billions in damages to companies.
Mitigation:
✅ Regularly back up data to external drives or cloud storage
✅ Avoid clicking on suspicious email links or attachments
✅ Keep operating systems and software updated
4. Denial-of-Service (DoS) & Distributed Denial-of-Service (DDoS) Attacks
Definition: These attacks overwhelm a system, website, or network with traffic to make it unavailable to users.
How It Works:
- Attackers use a botnet (infected devices) to flood a server with fake requests.
- The server becomes overloaded and crashes, disrupting services.
Mitigation:
✅ Use a Content Delivery Network (CDN) to handle traffic surges
✅ Enable DDoS protection services (Cloudflare, AWS Shield)
✅ Monitor network traffic for unusual spikes
5. Social Engineering Attacks
Definition: Social engineering manipulates people into revealing confidential information.
Types of Social Engineering:
- Pretexting – Impersonating an authority figure to gain information.
- Baiting – Offering something tempting (e.g., free software) to trick users into downloading malware.
- Tailgating – Gaining physical access to restricted areas by following an authorized person.
How It Works:
- An attacker pretends to be IT support, asking for a password reset.
- Victim unknowingly provides access, allowing attackers to steal sensitive data.
Mitigation:
✅ Verify identities before sharing information
✅ Train employees on social engineering awareness
✅ Use strict access controls for sensitive systems
6. Man-in-the-Middle (MitM) Attacks
Definition: A hacker intercepts and alters communication between two parties without their knowledge.
How It Works:
- A hacker intercepts Wi-Fi traffic on an unsecured network.
- They monitor or modify messages between users and services.
- Can lead to stolen login credentials, financial data, or altered transactions.
Mitigation:
✅ Avoid using public Wi-Fi without a VPN
✅ Enable HTTPS on websites
✅ Use end-to-end encryption for sensitive communications
7. Insider Threats
Definition: Threats that come from employees, contractors, or business partners who misuse their access to harm an organization.
Types:
- Malicious insiders – Employees with harmful intent steal or leak data.
- Negligent insiders – Careless employees accidentally expose sensitive information.
How It Works:
- An employee steals confidential files and sells them to competitors.
- A staff member accidentally emails sensitive customer data to unauthorized individuals.
Mitigation:
✅ Implement Role-Based Access Control (RBAC)
✅ Monitor unusual login activities
✅ Regularly conduct security training
8. Advanced Persistent Threats (APTs)
Definition: APTs are long-term, stealthy attacks often conducted by nation-states or organized cybercriminal groups.
How It Works:
- Attackers infiltrate a network undetected, gaining long-term access.
- They steal sensitive data over time, often remaining hidden for months or years.
Mitigation:
✅ Conduct regular cybersecurity audits
✅ Use threat intelligence services
✅ Segment networks to limit damage from breaches
9. Zero-Day Exploits
Definition: Attacks that exploit unknown software vulnerabilities before developers can patch them.
How It Works:
- Hackers discover a flaw in software before the vendor releases a fix.
- They exploit it to gain unauthorized access or cause damage.
Mitigation:
✅ Keep software and systems updated
✅ Use intrusion detection systems (IDS)
✅ Regularly check for vendor security patches

Support Us
Contact UsnnSupport Center
Contact Us
mouali.rachid@yahoo.comnn+1-216-334-377
Copyright © 2025 Rachid Mouali All Rights Reserved.